Your Crypto Wallet Is Leaking Your IP Before You Make a Key.
An independent researcher ran 13 web3 wallets through a clean Android device and a packet sniffer. Twelve of them phoned home before the user did anything. One didn't make a single DNS request.
You can hold the most private coin on Earth but none of it matters if the wallet you use pings forty servers the moment you open the app. By the time you tap "create wallet," your IP and your device fingerprint are already out the door, sitting in someone else's database, waiting to be matched to whatever you do next.
That's the finding from a network-traffic analysis published today on X by an independent researcher operating under the handle r4nk0X. Their setup was deliberately minimal: a clean Android device, no SIM, APKs pulled via gplaydl, traffic routed through a VPN, and PCAPdroid logging every packet on a per-app basis. Then they opened thirteen of the most popular web3 wallets, once each, and watched what each app said to the internet before the user said anything to it.
The scorecard runs from 0 to 100. 100 means zero IP exposure. The underlying metric is simple: unique remote IPs plus unique domains contacted on first launch.
The results split the field into three rough tiers.
At the bottom: SafePal (0/100) and OKX Wallet (7/100), the worst offenders. SafePal opens with around twenty chain RPC calls to providers like Alchemy, dRPC, and Thirdweb, plus integrations with Base, Optimism, Fantom, Blast, xLayer, Flare, Klaytn, and opBNB.
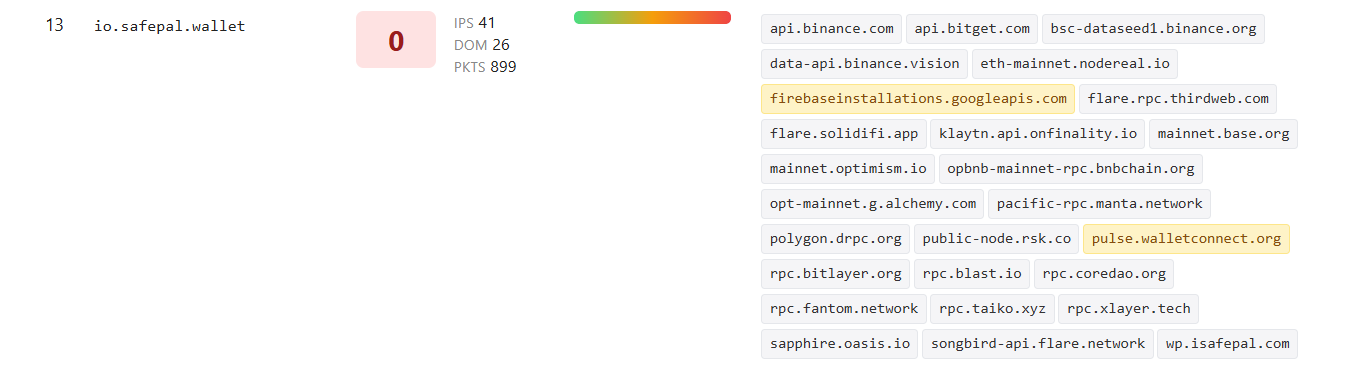
Every one of those endpoints sees the user's IP before a wallet exists. OKX Wallet ships eight AppsFlyer subdomains, four Amplitude variants, OneSignal push, three calls to online-metrix.net (a ThreatMetrix fingerprinting service), and a connection to an Alibaba Hong Kong endpoint. On a clean device. Without an account.

The middle tier is where most users live and don't know it. Crypto.com Wallet (49/100), Solflare (54/100), Base by Coinbase (55/100), and MetaMask (61/100) all carry heavy attribution and analytics stacks: AppsFlyer, Branch, Segment, Firebase, Crashlytics, Sentry, Braze, Customer.io, Intercom many of them firing simultaneously at cold start. MetaMask reaches Polymarket and Infura before the user does anything. Solflare loads two Intercom channels and two Customer.io endpoints, the cross-channel messaging infrastructure is set up to talk to you before you've even imported a seed phrase.
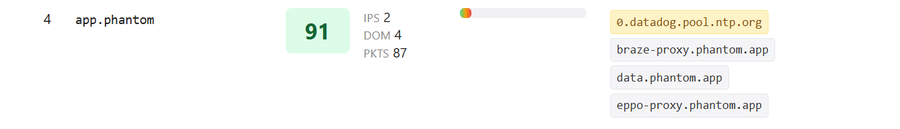
The top tier looks different. Phantom (91/100) routes its third-party services, Braze, Eppo, Datadog through its own *.phantom.app proxies, hiding the vendors from network observers.
Atomic Wallet (87/100) and Trust Wallet (79/100) lean on their own infrastructure with limited third-party leakage. Unstoppable (94/100) makes only two calls. Zodl (97/100) makes one. And Cake Wallet (100/100) makes none.
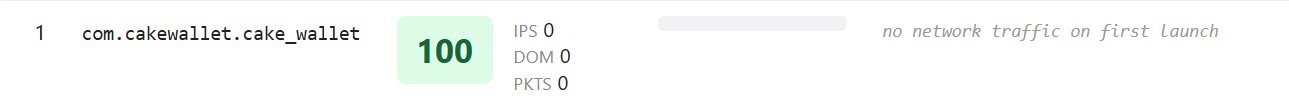
That's the bar. Cake Wallet, a wallet that focuses on ease of use and building trustless software generates zero DNS requests, zero domain contacts, zero outbound packets on first launch. The app opens, waits for the user, and does nothing else. Zodl, a Zcash wallet, contacts a single endpoint. Unstoppable contacts two: its own backend and WalletConnect telemetry.
The wallets at the top of the scorecard aren't doing something clever. They're just not doing the thing everyone else is doing. No Firebase calls home. No Segment pipeline collecting events. No AppsFlyer attribution. No Crashlytics, Sentry, Braze, or Amplitude waiting in the background. Most wallets ship with this stack baked in from day one, these don't. Privacy here is the default, because the surveillance was never wired up in the first place.
For users who care about anonymity at the network layer, journalists, activists and anyone whose threat model includes correlation between IP and wallet this matters more than chain support, more than UI, more than fees. A wallet that pings forty servers on launch has already broken the assumption that on-chain pseudonymity protects you. The link between your real-world identity and your on-chain activity gets made before you ever sign a transaction. Think about that.
The full methodology and per-wallet domain lists are public on r4nk0X's X thread. We'd recommend any web3 user audit their own wallet against the scorecard.
You can hold the most private coins on Earth so you better make sure your wallet isn't selling you out at the front door.